SAST vs. DAST: Key Differences & Security Guide
Feb 07, 2023
Neglecting security is a rookie mistake. However, DevOps teams struggle to make it a priority in the quest to be continuously faster. Protecting your app from the ground up is challenging, so you need the right tools to improve your debugging process in development and production.
To enhance security testing, developers can use SAST tools, which analyze program source code to identify security vulnerabilities, and DAST tools, which come up in later development phases in a running application. This article explains the SAST and DAST methods, including a comparison table of their main features and characteristics.
4 of the ways security tools help developers
The problem with security is that it’s never a one-time fix. Systems are constantly evolving, and new threats are always on the horizon. Security tools have become a critical part of software development as they help developers keep up with new threats. Here are some benefits they offer:
1. Reduce human error
82% of data breaches involve human intervention. Security tools can help minimize human error by scanning code for errors and misconfigurations before deployment and security drift after deployment.
2. Detect bugs faster
Security tools can help developers detect bugs faster by providing them with automated processes to identify potential security vulnerabilities in their code. For example, SAST tools can automatically identify potential security issues and provide developers with detailed reports on where these vulnerabilities are located and how to fix them.
Additionally, DAST tools can simulate real-world attacks on an application and give the developers feedback on how well their code holds up to these attacks.
3. Increase software quality
With reduced human error and the ability to detect bugs faster, developers can quickly identify and fix security vulnerabilities in their code, improving their applications’ overall reliability and security.
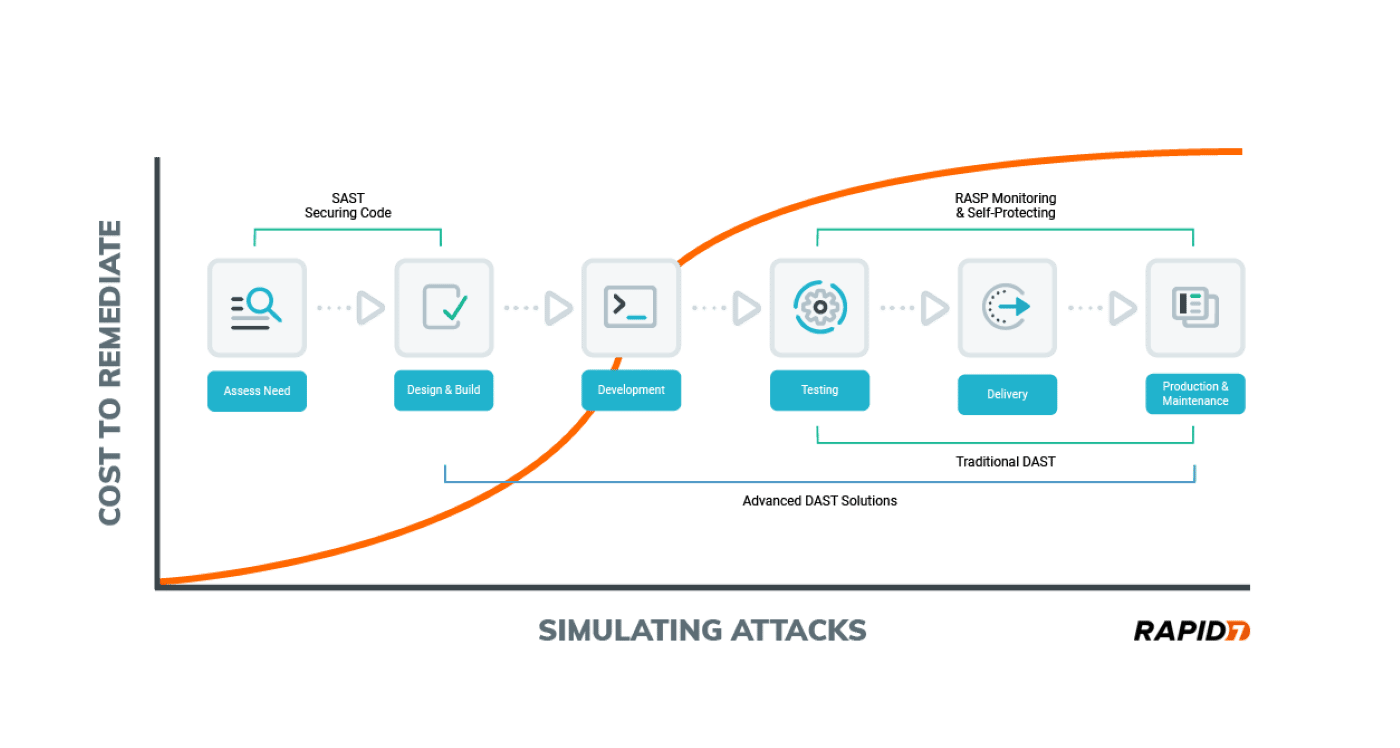
4. Reduce costs
When developers do not prioritize security in their SDLC, it is more expensive and time-consuming to fix when they find a vulnerability. With increased software quality, there will be reduced costs for resolving issues and more time spent developing new features.
What is SAST?
Static Application Security Testing (SAST) is a type of security testing used to identify security vulnerabilities in applications by analyzing source code without actually executing the code. SAST is a white-box testing method in which the software’s design is known to the tester.
SAST is performed early in the SDLC as part of a shift left testing approach. The goal is to prevent issues earlier, before going into production. SAST can be performed manually by a security expert who reviews the code or can be automated using specialized tools. These tools typically use algorithms and other techniques to identify code patterns indicative of security vulnerabilities.
SAST tools can help you identify critical vulnerabilities, including buffer overflows, SQL injection, and cross-site scripting.
3 Benefits of SAST
Some of the benefits of using SAST tools include the following:
1. Early detection of vulnerabilities
SAST can be performed early in the development process, allowing developers to identify and fix security vulnerabilities before they deploy the application. Detecting issues earlier can help prevent costly security breaches and reduce the overall risk to the organization.
2. Comprehensive coverage
SAST tools analyze the entire source code of an application, providing a comprehensive view of its security posture. The extensive coverage allows developers to identify vulnerabilities hidden in complex or hard-to-reach parts of the code.
3. Automated analysis
SAST tools are typically automated, so they can quickly and efficiently analyze large codebases. This efficiency allows developers to focus on other essential tasks, such as building new features or improving the user experience.
By identifying and addressing security vulnerabilities early in the development process, SAST can help organizations improve the overall security of their applications, protect sensitive data, maintain customer trust, and avoid costly security breaches.
What is DAST?
Dynamic Application Security Testing (DAST) is a type of security testing that analyzes an application while it is live to identify security vulnerabilities. As opposed to SAST, DAST is a black-box testing method as the tester doesn’t have access to the source code.
DAST works by simulating attacks on an application to mimic a malicious attacker. The goal is to find unexpected outcomes that attackers could use to compromise an application. Since DAST tools don’t have information about the application internals or source code, they work as an external threat, just like an actual attack would.
DAST tools can help you identify critical vulnerabilities such as:
- Insecure authentication and access control mechanisms allow unauthorized users to access sensitive data or perform actions they are not permitted to do.
- Insecure communications, such as unencrypted network connections or weak cryptography, enable an attacker to intercept and read sensitive data transmitted by the application.
- Unvalidated input enables an attacker to submit malicious data to the application that it is unprepared to handle, potentially leading to security vulnerabilities or application crashes.
5 Benefits of DAST
There are various benefits to using DAST, such as:
1. Testing in production
As there are always vulnerabilities and bugs after deployment, DAST tools like Lightrun can analyze your application while running, so you can identify vulnerabilities before they can be harmful.
2. Simulated attacks
DAST tools simulate attacks on an application, allowing organizations to see how the application responds to these attacks and identify vulnerabilities that may not be detectable using other testing methods.
3. Comprehensive coverage
Developers can configure DAST tools to test all aspects of an application, including the user interface, network communications, and underlying infrastructure. This coverage provides a more comprehensive view of the application’s security posture.
4. Continuous monitoring
You can use DAST tools to continuously monitor an application for potential vulnerabilities, allowing organizations to quickly identify and address any new security risks that arise.
5. Regulatory compliance
DAST can help organizations meet compliance requirements related to data security or industry-specific regulations.
Security tools for each stage of software development
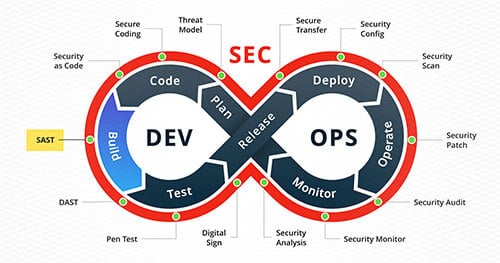
In recent years, rising cybercrime and cybersecurity issues have given rise to the new term “DevSecOps.” DevSecOps is based on the principles of collaboration, automation, and continuous improvement, to deploy secure software faster and more efficiently.
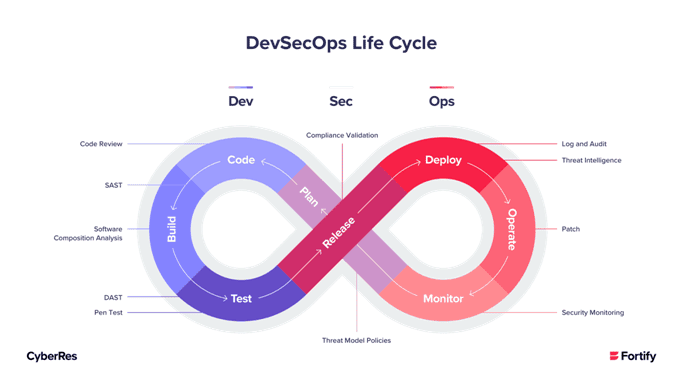
One of the critical components of DevSecOps is the “shift left” approach, which involves shifting security practices to the left (earliest stages) in the development process. Below is a list of each phase of the SDLC and the security tools required to protect that stage:
- Plan: Threat modeling tools that allow developers to identify potential security risks and prioritize their efforts accordingly.
- Code: Code review, SAST tools
- Build: Software composition analysis
- Test: DAST, IAST, penetration testing tools
- Release: Compliance validation tools
- Deploy: Logging, auditing, and threat intelligence tools
- Operate: Patching, RASP tools
- Monitor: Security Monitoring tools
SAST vs. DAST: what are the differences?
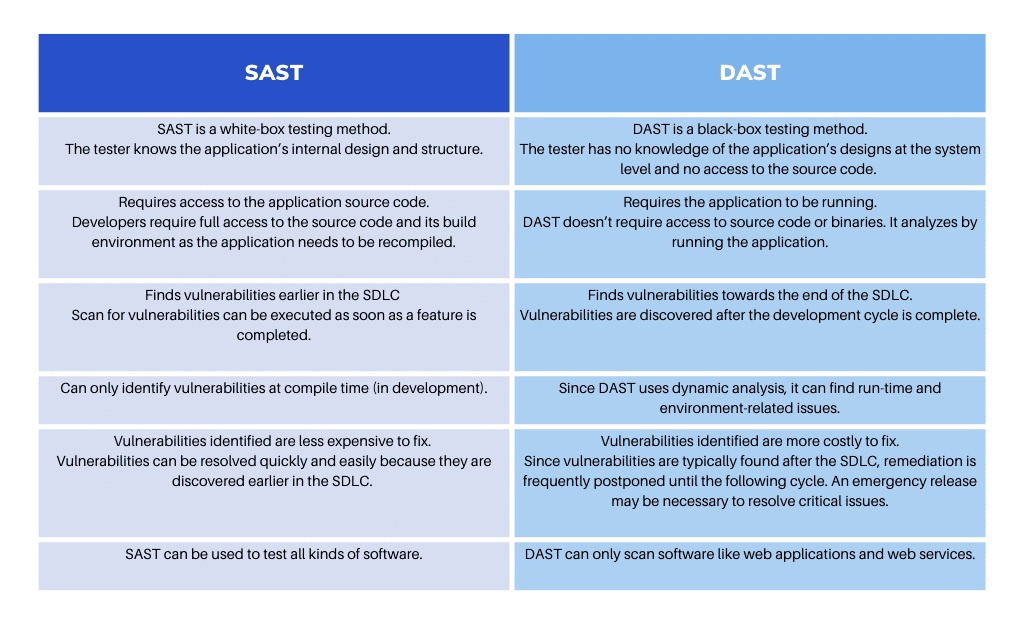
Both Static application security testing (SAST) and dynamic application security testing (DAST) can find vulnerabilities in an application. However, they are different in the following ways:
Why you need a continuous security approach?
DevOps teams must adopt a combined approach and use multiple tools to find vulnerabilities. No single tool can find all applications’ vulnerabilities, as different tools look for specific vulnerabilities.
By combining SAST tools that work in development and DAST tools for production, you can have a more comprehensive view of your application’s security posture and better understand the potential risks that your applications may face.
For tools that work in production, multiple features are necessary. For instance, they shouldn’t affect the app’s functionality or require troubleshooting, and they should make the DevOps team’s job easier rather than more complicated, reducing MTTR (Mean Time To Repair).
Taking your security testing to the next level
SAST and DAST should be a part of any developer’s toolkit. While in an ideal scenario, your code would be 100% clean once deployed – this rarely is the case. Thankfully, that’s exactly what DAST tools are for. Lightrun can help you add and monitor logs, traces, and metrics to your code in production without impacting the app’s functionality or having to troubleshoot it. Does this sound like a debugging dream? Request a demo with us today.



